AI guardrails are the rules and runtime checks that keep an AI system inside acceptable boundaries. In practice, that means filters, approvals, tool limits, escalation rules, and monitoring that decide what an agent can access, what it can say, what it can do, and when a human needs to step in.
Without guardrails, even a capable AI agent can create expensive problems. It might answer from the wrong source, expose sensitive data, trigger the wrong workflow, or take an action that should have required review. Good guardrails do not make an agent impressive in a demo. They make it trustworthy in production.
What AI guardrails actually mean
The simplest way to think about guardrails is this: they are the operational boundaries around an AI workflow. They are not the same as model quality, and they are not the same as governance.
- Model quality is about whether the model can reason, summarize, classify, or generate well.
- Guardrails are about whether the system stays inside the rules you set while it does that work.
- Governance is the broader operating model around ownership, policy, audit, approval, and lifecycle management.
That distinction matters because companies often buy a strong model and assume safety comes with it. It does not. A model can be smart and still be allowed to do the wrong thing in your environment.
In a real business setting, guardrails usually answer questions like these:
- Should this request be answered at all?
- Is the answer grounded in approved sources?
- Can the agent call this tool or API?
- Does this action need human approval first?
- Should sensitive data be blocked, masked, or logged?
- What should happen if confidence is weak or policy is unclear?
The main layers of a practical guardrail system
Most production systems need more than one guardrail. A single content filter is not enough if the agent can also search internal systems, send emails, modify records, or trigger downstream workflows.
AI guardrail layers that matter in production
| Layer | What it checks | Example |
|---|---|---|
| Input guardrails | Whether the incoming request is allowed, in-scope, and safe to process | Block a prompt asking for medical advice in a general HR bot |
| Data and retrieval guardrails | Which sources can be used and whether retrieved context is approved | Answer only from a policy library, not the open web |
| Tool and action guardrails | Which systems the agent can touch and under what conditions | Allow ticket lookup but require approval before refunds |
| Output guardrails | Whether the final answer contains unsafe, ungrounded, or disallowed content | Mask account numbers before a response is sent |
| Human approval and escalation | Whether a person must review high-risk actions or uncertain cases | Pause before cancelling a customer contract |
| Monitoring and audit guardrails | What gets logged, reviewed, measured, and improved over time | Track blocked actions, overrides, and repeated failure modes |
These layers work best together. If you only filter the final answer, you may still let the agent query the wrong database, perform an unsafe tool call, or waste time on tasks that should have been rejected at the start.
How guardrails work inside a real agent workflow
Imagine a customer support agent that can look up orders, offer refunds, and draft emails.
- The request comes in. Input guardrails check whether the request is in scope and whether it contains disallowed content.
- The agent gathers context. Retrieval guardrails limit which documents, systems, or records it can use.
- The agent decides on a next step. Tool guardrails determine whether it can look up an order, offer a discount, or issue a refund.
- High-risk actions pause. If the refund exceeds a threshold or the account looks unusual, the workflow requires human approval.
- The response is reviewed. Output guardrails check for sensitive data leakage, policy violations, or unsupported claims.
- The run is logged. Monitoring records what was blocked, approved, escalated, or retried so the system can improve.
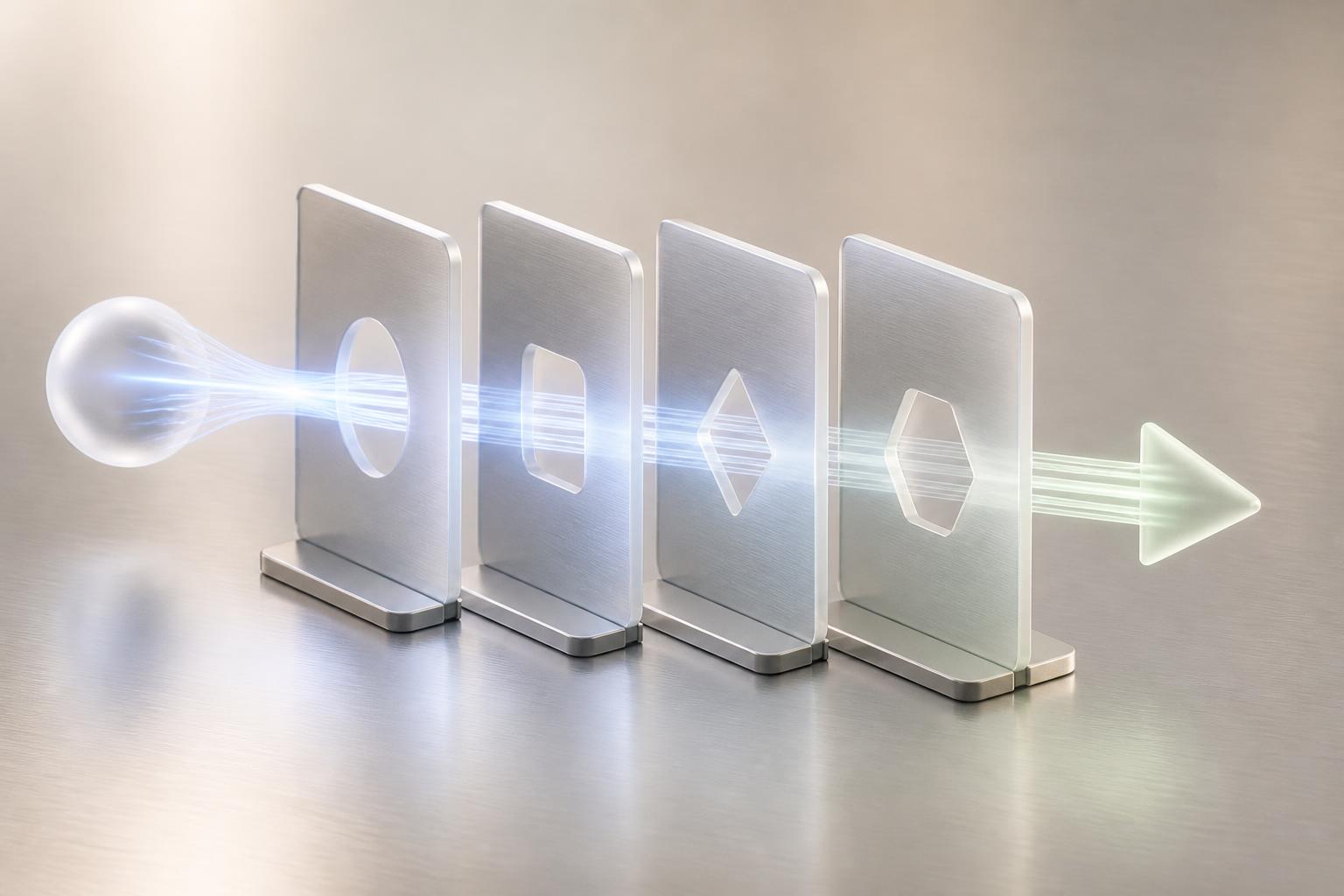
The key point is that guardrails are not one thing at the end. They are checkpoints throughout the workflow.
How to implement AI guardrails without making the system useless
The mistake many teams make is trying to design a perfect safety architecture before they have one useful workflow. A better approach is to start with one valuable process and add the minimum guardrails needed for that process to be trustworthy.
1. Start with one workflow, not a whole department
Pick a narrow job such as support triage, invoice review, lead qualification, or internal policy Q&A. Guardrails are much easier to design when the workflow has a clear boundary.
2. Define the non-negotiables
Write down what the agent must never do. Examples include exposing PII, approving payments, answering outside approved sources, changing system records without authorization, or pretending confidence when it is uncertain.
3. Match each risk to a specific control
Do not solve every risk with the same mechanism. A bad answer from weak retrieval needs a different control than a dangerous tool call.
- If the risk is unsafe input, use input filtering and scope checks.
- If the risk is bad evidence, use retrieval limits and source validation.
- If the risk is harmful actions, use tool permissions, thresholds, and approvals.
- If the risk is bad final output, use output checks and fallback behavior.
4. Add human approval where judgment or liability is high
Not every action needs review. But some clearly do: refunds above a threshold, contract changes, publishing external communications, security changes, regulated advice, or anything irreversible. Human-in-the-loop does not mean the agent failed. It means the workflow knows where automation stops being safe.
5. Design graceful fallback behavior
A blocked action should not leave the user in a dead end. The system should know whether to ask a clarifying question, hand off to a human, provide a safe refusal, or route the case into a queue.
6. Test failure modes before launch
Run the workflow against edge cases, adversarial prompts, missing data, contradictory instructions, and ambiguous approvals. If your team only tests happy paths, your guardrails are probably too optimistic.
Common mistakes that make AI guardrails fail
- Treating guardrails as only a content moderation problem. Many failures happen at the action layer, not the language layer.
- Adding guardrails only after the system is already live. Retrofitting controls is harder than designing them into the workflow.
- Using one blanket policy for every workflow. A customer support bot, an internal analyst, and an invoice agent do not need the same boundaries.
- Blocking too aggressively. If the system refuses too often, teams bypass it and trust falls anyway.
- Ignoring false negatives and false positives. A guardrail that misses harmful behavior is a risk, but a guardrail that blocks legitimate work is an operational problem too.
- Forgetting observability. If you cannot see what got blocked, approved, or escalated, you cannot improve the system.
AI guardrails vs AI evals vs AI governance
These concepts work together, but they are not interchangeable.
- Guardrails enforce boundaries during runtime.
- Evals measure whether the system behaves the way you want across test cases.
- Governance defines ownership, policy, controls, approvals, and accountability across the program.
A useful mental model is this: evals tell you whether the system is performing well, guardrails help stop bad behavior while it runs, and governance determines who is responsible for the rules and what happens when the system breaks them.
A practical checklist before you ship
- Define the exact workflow, user group, and allowed outcomes.
- List the actions the agent can take and mark which ones need approval.
- Restrict the data sources and tools to the minimum needed.
- Set rules for sensitive data handling, redaction, and logging.
- Decide what the agent should do when confidence is low or evidence conflicts.
- Test blocked prompts, bad retrieval, unsafe tool calls, and incomplete outputs.
- Instrument the workflow so you can review escalations, overrides, and repeat failures.
- Assign an owner who updates the rules as the workflow changes.
The best AI guardrails do not make an agent feel restricted. They make it dependable. If users know where the system is strong, where it pauses, and when a human will step in, adoption usually improves because the workflow feels safer and more predictable.
That is the real goal: not maximum autonomy, but useful automation that stays inside business reality.